CERT-In Warns Orgs to Watch Out for Multiple Vulnerabilities in Google Chrome
The Indian Computer Emergency Response Team (CERT-In) has issued a high-severity warning to organizations, urging them to watch out for multiple vulnerabilities in Google Chrome that allows hackers to bypass security restrictions on targeted systems.
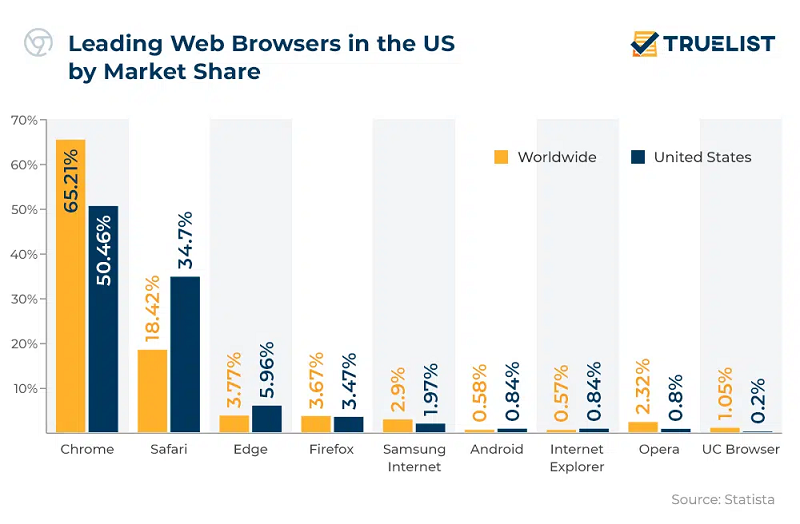
CERT-In has discovered a plethora of vulnerabilities in Google Chrome (one of the widely used browsers across the world) that could provide attackers with access to users’ data and even execute arbitrary codes by dodging all security restrictions. Though the vulnerability has not affected all Chrome users, the scope of risk is quite huge considering the wide use of the browser worldwide, says CERT-In.
Google has acknowledged the vulnerabilities and bugs and has stated that it is working to fix all the bugs. Further, the tech giant urged users all over to download the latest Chrome OS to be on the safer side.
Why is this a topic of concern for businesses?
As per CERT-In, the attacker could further exploit the vulnerability by sending out specially crafted access requests targeted toward critical systems in an organization. Simply put, the vulnerability is being exploited in the wild, said CERT-In. The central organization said that the vulnerability could be further used to trick a victim into clicking or opening a malicious file thus, allowing access to internal networks and user data.
Read also: CERT-In Mandatory Guidelines for Security Breaches
Key Takeaways and Lessons Learned from the Log4j Vulnerability
These vulnerabilities could allow cybercriminals to unleash denial of service (DoS) attacks on targeted systems. Such an attack could lock out the users from accessing information devices, systems, and other critical IT resources affecting an organization’s operations. Hackers could target websites, email accounts, etc. through such attacks thus, disrupting business processes.
How cybercriminals attack web browsers?
Cybercriminals utilize a number of hack tactics to exploit vulnerabilities in web browsers. Hackers discover a vulnerability or bug that allows them to download and run malicious codes (often after a user visits or clicks on a compromised URL or file). Next, the code can auto download or run various other malicious codes or steal sensitive business information.
Read also: Hackers exploit endpoint vulnerability to hack servers of a leading bank in India
Another common tactic used by hackers is ‘phishing’. Here, attackers send phishing emails that contain exploit kits targeted toward web browsers. In fact, phishing was found to be the most prominently used attack tactic in 90% of such breaches, says CISCO. Victim clicks on a link or attachment in the mail, which opens up a malicious page in their web browser, which can then exploit an unpatched vulnerability to deploy malware packages or steal browser data. Timely vulnerability assessment and management can save the day here.
Futurism Advisory: How business can mitigate cyber risks from web browser vulnerabilities?
Businesses ought to blend in a mix of techniques that involve people, process and technology to mitigate and respond to browser vulnerabilities. It starts with cybersecurity hygiene at workplace.
Keeping browsers updated all the time
Clearing browser history regularly to erase stored credentials or passwords
Clearing cookies as these can allow hackers to access email services without a user’s credentials
Most browsers unfortunately are vulnerable to Zero Day attacks – reason being that a good number of users simply don’t like to reboot their web browsers, which is the first and foremost aspect of an update.
Next, businesses can enforce a powerful identity and access management mechanism with multifactor authentication on all mission-critical systems and workstations. This will prevent attackers from accessing these systems even if they manage to steal the credentials. Most importantly, ensure that the IT team can execute all these tasks remotely with ease. Better, they can automate these tasks by partnering with a trusted cyber security services provider.
Last but not the least, roll out an enterprise-wide cybersecurity awareness program that is designed to educate all the employees about best cybersecurity practices and why everybody needs to follow them. A trusted managed email security provider will not only help you deploy a powerful line of cyber defense from coming-of-age web attacks, but would also train employees to spot novel phishing attack tactics including spear-phishing, multi-prong attacks, and identify new strands of Ransomware. They will also educate them on safe browsing practices.
Takeaway
Managing browser vulnerability risks go beyond patching and opting for expert cyber security services is the smartest thing a business can do to keep such attacks at bay. Browsers enable users to access all types of content, which is why they are a hot target for attackers worldwide. Our managed endpoint security services offer a fine mix of mobile device management solutions and web security services to protect businesses from browser-based attacks by helping them deploy a solid layer of a web defense that is backed by market-leading and advanced threat intelligence tech (IBM), executed by certified cybersecurity engineers and experts, and delivered from a state-of-the-art SOC.
Disclaimer: All the information, opinions and views expressed in this article are those of the web authors and their respective sources and in no way reflect the principles, objectives or views of Futurism Technologies.
Futurism Technologies is a trusted Digital Transformation (DX) advisor and consulting partner helping businesses around the world to unlock the true value of digital for the last two decades. One of the fastest-growing global digital transformation companies with offices across continents including North America, Europe, the Gulf, Asia, and Australia, Futurism delivers 360-degree Digital Transformation solutions to enterprises of all sizes and verticals. We have been helping enterprises leverage advanced technologies with our tested DX solutions. Futurism takes great pride in helping businesses realize the true potential of digital by helping them leverage the most from coming-of-age technologies such as Artificial Intelligence (AI), Machine Learning (ML), Robotic Process Automation (RPA), 5G, IoT, Data Science/Big Data, Cybersecurity, Blockchain, Mobility, Product Engineering, Cloud, and more.
Make your business more successful with latest tips and updates for technologies